Picture this. A quiet street. No witnesses. No clear motive. Just a locked room and a question no one can answer.
At first, it feels like a dead end. No fingerprints that matter. No one saw anything. Nothing obvious to follow.
But then someone notices a phone.
Not the person. Not the room. The phone.
It’s just sitting there. Screen dark. Looks harmless. Almost irrelevant. But here’s the thing. That small device has been quietly recording a story the whole time.
Call logs. Last messages. Location pings. Even the time the screen was last unlocked. Piece by piece, it starts filling in the gaps that people couldn’t.
This is where digital evidence steps in.
Not as something complicated or technical. Think of it like invisible footprints. Every tap, every swipe, every connection leaves behind a trace. You don’t see it at first, but once you start looking, it’s everywhere.
And in cases where humans forget, lie, or simply aren’t there, these traces often become the most honest witness in the room.
That’s the shift. Investigations are no longer just about what people saw. They’re about what devices remember.
And more often than not, they remember everything.
What Counts as Digital Evidence?
Now let’s make this simple.
Digital evidence is any data that is created, stored, or shared using electronic devices. That’s it. No heavy definitions needed.
Think of it like footprints in sand. Every action leaves a mark. The only difference is, these footprints exist inside devices instead of on the ground.
You send a message. There’s a record.
You open an app. There’s a log.
You move from one place to another with your phone. There’s a trail.
Most of the time, we don’t notice it. But those tiny traces quietly build a timeline of what actually happened.
And here’s where it gets interesting. This kind of data doesn’t come from just one place. It’s everywhere.
Your smartphone is one of the biggest sources. Calls, chats, photos, app activity. It holds a detailed snapshot of your daily life.
Laptops and computers add another layer. Browsing history, downloaded files, login records. All of it can be tracked and analyzed.
Then comes cloud storage. Even if something is deleted from a device, it might still exist online. Backups, synced files, shared folders. They often keep copies people forget about.
Emails are another strong source. Not just the content, but timestamps, sender details, and hidden metadata that reveal more than what’s visible.
And finally, there are CCTV systems and IoT devices. Cameras, smart home gadgets, even fitness trackers. They continuously record activity in the background.
What this really means is simple. Digital evidence isn’t rare. It’s constant. It’s being created every second, often without us even realizing it.
Types of Digital Evidence You See in Real Cases
Once you understand what digital evidence is, the next step is seeing how it shows up in real investigations.
It’s not just one kind of data. It comes in layers. Each layer tells a different part of the story.
Let’s break it down.
Communication Data
This includes messages, emails, and call logs. Basically, anything people use to talk or connect.
In many cases, this is where the first clue appears. A deleted message, a late night call, or an email that doesn’t match the timeline.
For example, a suspect might claim they had no contact with someone. But call records show multiple conversations just hours before the incident. Even if messages are deleted, forensic tools can often recover parts of them or show that communication existed.
What people say and when they say it often reveals intent.
Location Data
This is all about movement. GPS data, cell tower connections, and app location history.
Phones constantly interact with networks, leaving behind a trail of where they’ve been.
Imagine someone claims they were at home all night. But their phone connects to towers across town during that same time window. That mismatch becomes a critical clue.
Even small location pings can help rebuild a person’s journey step by step.
Multimedia Files
Photos, videos, and audio recordings fall into this category. But the real value often comes from metadata.
Metadata is hidden information stored inside files. It can include time, date, device details, and sometimes even location.
For instance, a photo might look ordinary. But its metadata shows it was taken at a specific place and time that contradicts a statement. That single file can shift the entire direction of a case.
System Logs
These are records created by devices themselves. Login times, file access, app usage, and system activity.
They may not look exciting, but they are incredibly reliable.
Let’s say someone claims they never opened a certain file. System logs might show the exact time it was accessed, edited, or transferred. It’s like a silent record keeper that tracks every action without bias.
Network Evidence
This includes IP logs, browsing history, and online activity across networks.
Every time a device connects to the internet, it leaves behind identifiers.
In real cases, this can link a person to a specific action. For example, accessing a website, sending data, or logging into an account from a particular location.
Even if someone tries to hide their identity, network traces often leave enough clues to connect the dots.
What this really shows is simple. Digital evidence is not just one piece of proof. It’s a collection of small signals. When you connect them, they form a clear and often undeniable story.
Case 1: Mobile Phone That Solved a Crime
It started like many cases do. Confusion. Silence. And a suspect who seemed a little too confident.
He claimed there was no contact. No conversation. No reason to be connected to the victim at all. And on the surface, it looked clean. His phone showed nothing. No messages. No call history. Everything wiped.
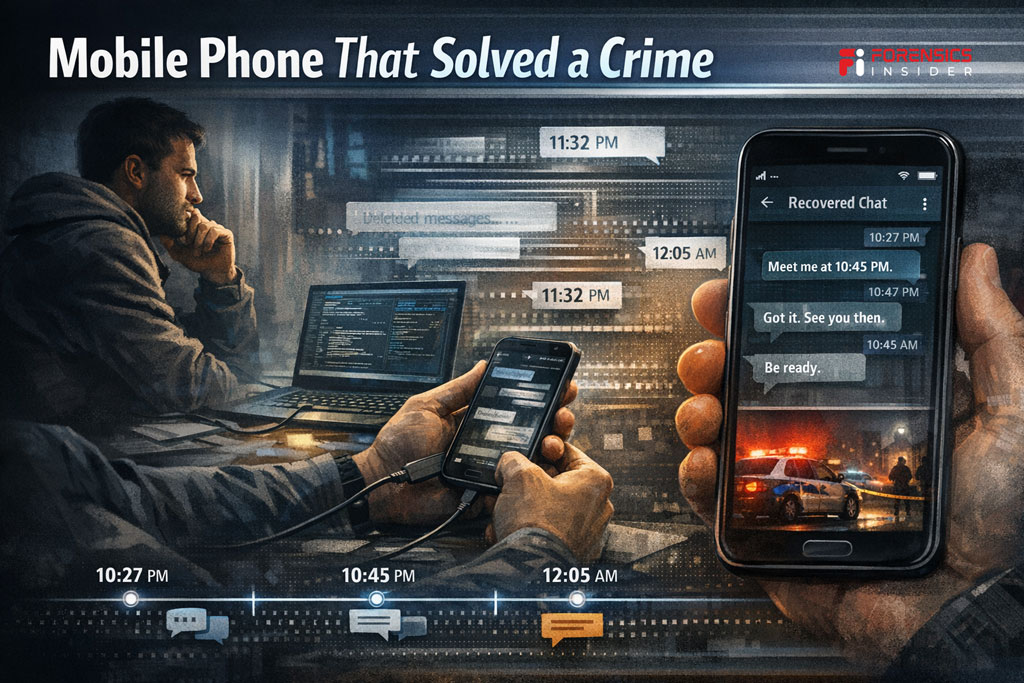
At first glance, it worked.
But here’s where digital evidence changed everything.
Investigators didn’t rely on what was visible. They went deeper. Using mobile forensic tools, they examined the device beyond the surface level. And slowly, fragments started to appear.
Deleted messages. Partial chat logs. Timestamps that didn’t match the story.
It wasn’t a full conversation at first. Just broken pieces. But even those pieces had a pattern.
A message sent late at night. Another one shortly after. Then silence. Then activity again.
When they reconstructed the timeline, something became clear. There was communication. Not random, not accidental. Consistent and recent.
The suspect’s version of events started to fall apart.
And then came the turning point.
A recovered chat thread showed a conversation just hours before the incident. The tone, the timing, the context. It connected everything. What was denied earlier now had proof.
That one phone, which looked empty at first, turned into the most reliable witness in the case.
This is the power of digital evidence.
Even when someone tries to erase the story, traces often remain. And when those traces are pieced together carefully, they don’t just support the investigation. They redefine it.
Case 2: Location Data That Told the Truth
This case looked simple on the surface.
The suspect had a clear statement. He said he never left home that night. No witnesses placed him outside. No cameras caught him. It almost felt like there was nothing to challenge.
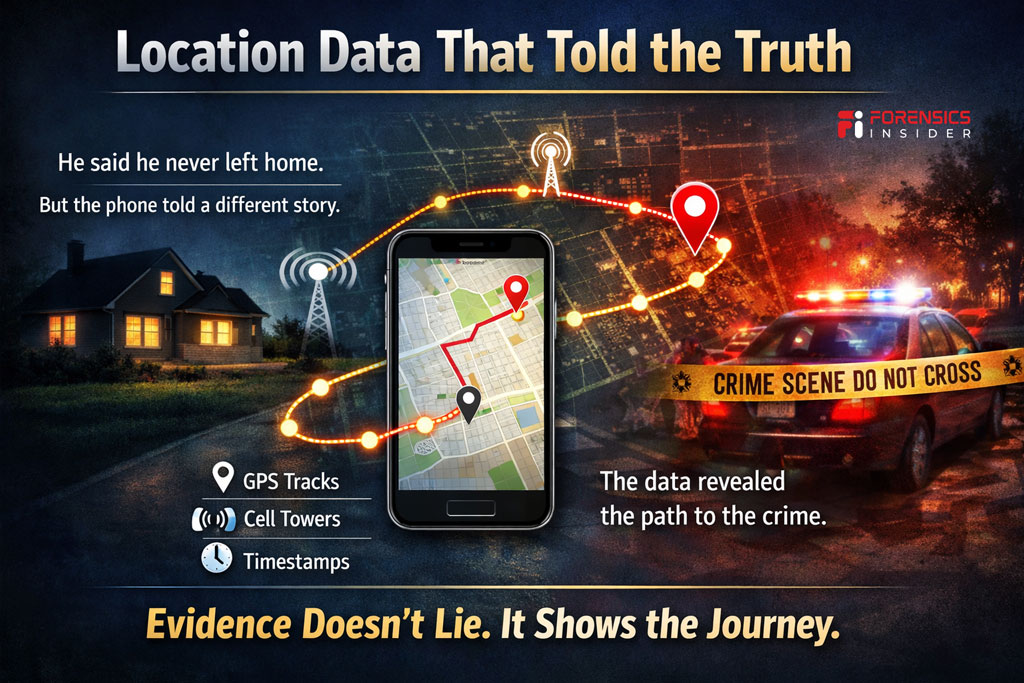
Until investigators checked the phone.
Not the messages this time. The movement.
Every smartphone quietly tracks location in the background. GPS signals, app activity, and cell tower connections all leave behind tiny markers. Alone, they don’t say much. But together, they tell a story.
When analysts pulled the location data, the first clue appeared. A timestamp showing movement late at night. Not inside the house, but moving away from it.
At first, it was just a single data point. Easy to ignore. But then more followed.
A pattern started forming.
The phone connected to different cell towers across the city. Each connection placed it farther from the claimed location. GPS logs showed stops along the way. Short pauses. Then movement again.
It wasn’t random. It looked like a route.
When they mapped it out, the path led directly toward the crime scene. The timing matched almost perfectly with the incident window.
Now the story had a problem.
The suspect said he stayed home. The data showed a clear journey outside. And not just once. The return path was also visible, placing him back home shortly after.
This is where digital evidence becomes hard to argue with.
It doesn’t rely on memory. It doesn’t get nervous or change its version. And, It simply records what happened.
By combining timestamps, GPS data, and network signals, investigators built a timeline that was far more reliable than any statement.
And in that moment, the truth wasn’t based on what was said.
It was based on where the device had been.
Case 3: Emails and Metadata That Revealed Intent
This case didn’t start with a crime scene. It started with a document.
A deal had gone wrong. Money was missing. And the person in question claimed it was all a misunderstanding. According to him, there was no intent to deceive. Just poor timing and confusion.
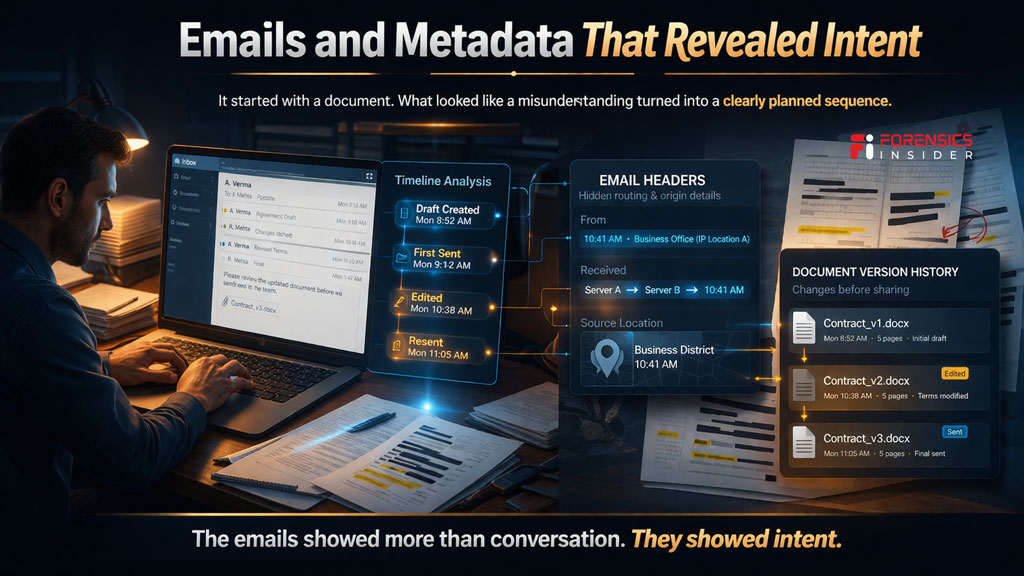
On the surface, it almost made sense.
Then investigators opened the emails.
At first, everything looked normal. Polite conversations. Regular updates. Nothing aggressive or suspicious. But digital evidence isn’t just about what you read. It’s about what sits behind it.
They began with timestamps.
Each email carried a precise record of when it was sent, received, and sometimes even drafted. When these were lined up, a pattern appeared. Messages that were claimed to be “after the fact” were actually sent much earlier.
That alone raised questions.
Then came the headers.
Email headers reveal routing paths, servers, and hidden technical details. They showed where the emails originated and how they traveled. In this case, they confirmed the messages were sent from specific locations that matched key moments in the timeline.
But the real turning point came from documents.
Attached files weren’t just static pieces of information. They carried version history. Edits. Changes made over time. Investigators found that certain documents had been modified just before being shared, with key details altered.
Now the story shifted.
What was presented as an honest mistake started to look planned.
When they combined the email trail, timestamps, and document history, a clear sequence emerged. Communication wasn’t random. It was structured. Timed. Intentional.
This is where digital evidence becomes powerful in a different way.
It doesn’t just show what happened. It shows why it happened.
And in cases like this, intent is everything.
Case 4: CCTV and Digital Footprints Working Together
This case didn’t rely on one source. It relied on everything working together.
There was CCTV footage. But it wasn’t perfect. A figure appeared on camera near the scene, but the face wasn’t clear enough to confirm identity. It created suspicion, not proof.
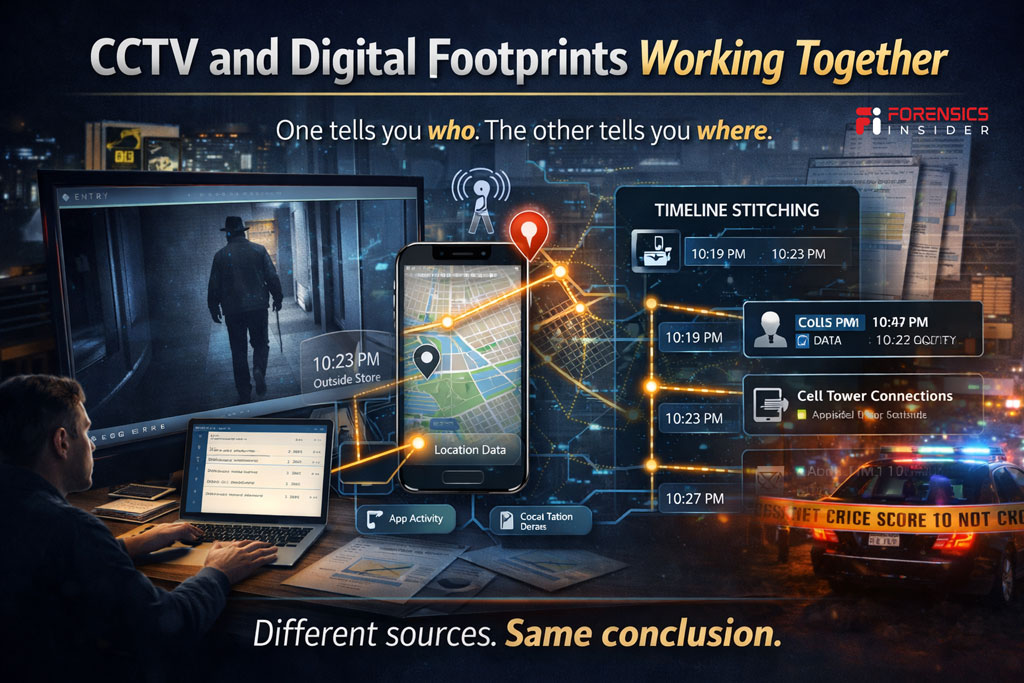
On its own, it wasn’t enough.
So investigators turned to digital evidence from devices.
They started with the timestamp from the CCTV clip. Exact time. Exact location. That became the anchor point.
Then they checked nearby mobile data.
Phones connected to towers in that area during the same time window were analyzed. One device stood out. It appeared near the location right when the footage was recorded.
Still, that alone wasn’t enough.
So they went further.
App activity logs showed the device was active just minutes before and after the CCTV capture. Location data confirmed short movements around the same spot. Not passing by. Staying within range.
Now the pieces started to align.
CCTV showed presence. Device data confirmed proximity. Timestamps matched across both sources.
This is called timeline stitching.
Instead of relying on a single piece of proof, investigators layer multiple data points on top of each other. Each one strengthens the other. Each one reduces doubt.
To make sure nothing was assumed, they cross checked everything.
The CCTV time matched the phone’s activity logs. The movement pattern matched the camera angle and entry point. Even network records supported the same sequence.
At that point, the gap between suspicion and certainty started to close.
This is where digital evidence becomes powerful in a combined form.
One source might raise questions. But when multiple sources tell the same story, it becomes very hard to challenge.
Not because one piece is perfect.
But because everything fits together.
How Investigators Actually Work With Digital Evidence?
Up to now, you’ve seen what digital evidence can do. Now let’s step behind the scenes and see how it’s actually handled.
Not like a textbook. Think of it like a journey.
Step 1. Collection
Everything starts at the scene.
Investigators don’t just grab devices and switch them on. That would risk changing or losing data. Instead, they carefully identify what might hold digital evidence.
A phone on a table. A laptop in sleep mode. A CCTV system quietly recording in the background.
Each device is handled with caution. Sometimes they’re powered down in a controlled way. Sometimes they’re isolated to prevent remote access. The goal is simple. Capture the data without altering it.
Because even a small change can affect what comes next.
Step 2. Preservation
Once collected, the focus shifts to protection.
Here’s the thing. Digital evidence is fragile. It can be modified, overwritten, or even lost if not handled properly.
So instead of working on the original device, investigators create an exact copy. A forensic image. Bit by bit, everything is duplicated.
This copy becomes the working version.
At the same time, they document everything. When the device was found. Who handled it. What was done to it. This creates a chain of custody.
It ensures that the data remains trustworthy from start to finish.
Step 3. Analysis
This is where the real story starts to unfold.
Investigators dig into the copied data using specialized tools. They don’t just look at what’s visible. They look at what’s hidden.
Deleted messages. File history. Login times. Location patterns.
It’s like assembling a puzzle. One piece might not mean much, but when multiple pieces come together, a clear picture starts to form.
They build timelines. Compare actions. Look for inconsistencies.
And slowly, the digital evidence begins to speak.
Step 4. Reporting
Finding the truth is only part of the job. Explaining it clearly is just as important.
Investigators turn their findings into reports that others can understand. Lawyers, judges, even people with no technical background.
No complex jargon. Just clear explanations.
What was found. How it was found. Why it matters.
Because in the end, digital evidence isn’t just about data.
It’s about telling a story that holds up when it really counts.
Challenges in Digital Evidence
Up to this point, it might feel like digital evidence always gives clear answers.
It doesn’t.
There are real challenges behind the scenes. And if you ignore them, you miss how complex these investigations actually are.
Let’s keep it practical.
Data Tampering
Digital data can be changed. That’s the first problem.
Files can be edited. Logs can be altered. Even timestamps can be manipulated in some cases.
So investigators don’t just trust what they see. They verify it.
They look for inconsistencies. Compare multiple sources. Check if the data behaves naturally or looks forced.
Because one altered file can mislead an entire investigation if it’s not questioned properly.
Encryption
Now imagine the data is there, but locked.
Modern devices use strong encryption. Phones, apps, even cloud storage protect data with layers of security.
That’s great for privacy. But it creates challenges during investigations.
If access is restricted, analysts may not be able to read the content directly. They have to rely on indirect clues. Patterns, metadata, or legally approved access methods.
Sometimes, the data exists but stays out of reach.
Massive Data Volume
Here’s something people don’t expect.
There’s often too much data.
One smartphone alone can hold thousands of messages, images, app logs, and system records. Add laptops, cloud backups, and network logs, and it quickly becomes overwhelming.
The challenge is not just finding data.
It’s finding the right data.
Investigators need to filter, sort, and focus on what actually matters. Otherwise, important clues can get buried under irrelevant information.
Legal and Privacy Concerns
This is where things get sensitive.
Not all data can be accessed freely. There are laws, permissions, and privacy boundaries that must be respected.
Even if digital evidence could help, it cannot be collected or used without proper authorization.
Investigators have to balance two things. Getting the truth and following the law.
If that balance is broken, the evidence may not even be accepted later.
What this really shows is simple.
Digital evidence is powerful, but it’s not effortless.
Behind every clear conclusion, there’s careful handling, constant verification, and a lot of restraint.
Why Digital Evidence Matters More Than Ever?
Take a step back for a second.
Look at how we live now. Messages instead of letters. Online payments instead of cash. Navigation apps instead of asking for directions. Almost everything we do touches a device at some point.
And every one of those actions leaves a trace.
That’s why digital evidence has become so important.
Not because technology is complex. But because our lives are deeply connected to it.
A single login. A short message. A quick location ping. On their own, they might seem insignificant. Easy to ignore.
But when placed in the right context, even the smallest data point can change the direction of an entire case.
A timestamp can break an alibi.
A photo’s metadata can confirm presence.
A simple connection to a network can place someone at a critical location.
These aren’t dramatic clues. They’re quiet ones.
And that’s exactly why they matter.
Modern investigations are no longer built only on what people say or remember. They are built on what systems record consistently in the background.
This shift has changed how truth is established.
Instead of relying on a single piece of proof, investigators now work with layers of digital evidence. Each layer adds clarity. Each layer reduces uncertainty.
What this really means is simple.
The more our lives move into digital spaces, the more those spaces start holding our stories.
And in situations where facts matter most, those stories often become impossible to ignore.
Common Myths About Digital Evidence
Let’s clear a few things up.
There’s a lot of misunderstanding around digital evidence. Movies and headlines make it look either too easy or too perfect. The truth sits somewhere in the middle.
Myth 1. Deleted Data Is Gone Forever
This is one of the biggest misconceptions.
When something is deleted, it often isn’t immediately erased. In many cases, the system just marks that space as available. The actual data can still exist until it gets overwritten.
That’s why investigators can sometimes recover messages, files, or fragments that were thought to be gone.
But here’s the catch.
Recovery isn’t guaranteed. If new data replaces the old data, it may be lost for good. So while digital evidence can bring back deleted information, it depends on timing and conditions.
Can Police Recover Deleted CCTV Footage?
Myth 2. Only Experts Can Understand It
It’s true that deep analysis requires technical skill.
But understanding digital evidence at a basic level isn’t as complicated as it sounds.
Think about it. You already understand timestamps, messages, photos, and locations in your daily life. Investigators are working with the same elements, just in a more structured way.
The real expertise lies in how these pieces are collected, verified, and connected.
So no, it’s not something only experts can “see.”
But yes, it takes experts to interpret it correctly in a legal context.
Myth 3. It Is Always 100 Percent Accurate
This is where expectations need to be realistic.
Digital evidence is strong, but it’s not perfect.
Data can be incomplete. Devices can malfunction. Time settings can be wrong. And in some cases, information can be manipulated.
That’s why investigators never rely on a single source.
They cross check. They compare. And, They validate using multiple data points before reaching a conclusion.
Because the goal isn’t just to find data.
It’s to find reliable data.
What this really comes down to is simple.
Digital evidence is powerful, but it’s not magic. It works best when it’s understood clearly, handled carefully, and questioned when needed.
Final Takeaway
If there’s one thing to hold on to, it’s this.
Every action leaves a trace.
Not always visible. Not always obvious. But it’s there. Quietly recorded in devices, systems, and networks we use every day.
That’s what makes digital evidence so powerful.
It doesn’t rely on memory. It doesn’t get influenced by pressure. And, It simply reflects what happened, piece by piece.
Across the cases you’ve seen, one pattern stands out.
A deleted message that wasn’t really gone.
A phone that moved when someone said they didn’t.
An email trail that revealed intent.
A camera clip supported by device data.
Each one started small. Almost insignificant. But when those small pieces came together, they told a clear and consistent story.
And that’s the real shift.
Modern investigations are no longer built on a single moment or a single clue. They are built on layers of digital evidence, connected carefully to reveal the truth.
What this really means for you is simple.
Be aware.
Because whether it’s a phone in your pocket or a system you log into, data is being created constantly. Most of the time, it helps. Sometimes, it protects. And in critical moments, it speaks louder than anything else.
Not by being dramatic.
But by being precise.